
-
 McIlroy fights for repeat as last-round Masters drama begins
McIlroy fights for repeat as last-round Masters drama begins
-
Buttler keeps form as Gujarat ease past Lucknow in IPL

-
 Trump orders US naval blockade of Strait of Hormuz
Trump orders US naval blockade of Strait of Hormuz
-
Polls open as Peru picks ninth president in a decade
-
 US-Iran talks fail as world urges respect for truce
US-Iran talks fail as world urges respect for truce
-
Ukraine, Russia accuse each other of Easter truce violations

-
 Cape Town mayor elected to lead S.Africa's second-largest party
Cape Town mayor elected to lead S.Africa's second-largest party
-
Justin Bieber reconnects with fans on Coachella's second day

-
 Crippa, Demise claim Paris marathon victories
Crippa, Demise claim Paris marathon victories
-
Union Berlin appoint first female coach after Baumgart sacking

-
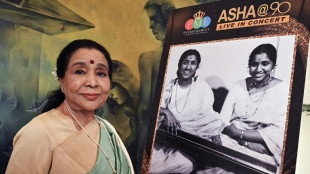 Legendary Indian singer Asha Bhosle dies aged 92
Legendary Indian singer Asha Bhosle dies aged 92
-
Finance minister favourite as Benin votes for president

-
 Imagine Dragons frontman chases childhood video game dream
Imagine Dragons frontman chases childhood video game dream
-
Teenage sprint star Gout powers to 200m win in blistering 19.67sec

-
 China's energy strategy pays off as Mideast war cramps supplies: analysts
China's energy strategy pays off as Mideast war cramps supplies: analysts
-
Hungarians vote in closely watched election, with Orban's rule on line

-
 Mideast war takes a bite out of Filipino street food vendors
Mideast war takes a bite out of Filipino street food vendors
-
Crime-weary Peru votes for ninth president in a decade

-
 Vance says talks failed to reach deal with Iran on ending Mideast war
Vance says talks failed to reach deal with Iran on ending Mideast war
-
New York's teen spirit frustrates Messi, Miami

-
 Vance says talks failed to reach agreement with Iran
Vance says talks failed to reach agreement with Iran
-
'Stop hiring humans'? Silicon Valley confronts AI job panic

-
 Force rue missed opportunities after another Super Rugby defeat
Force rue missed opportunities after another Super Rugby defeat
-
Ireland's Lowry becomes first with two Masters aces

-
 'Mental toughness' hailed after Reds snap 15-year Crusaders curse
'Mental toughness' hailed after Reds snap 15-year Crusaders curse
-
Justin Bieber fans flood Coachella festival for headlining show

-
 Saturday charge has Young in sight of first major title at Masters
Saturday charge has Young in sight of first major title at Masters
-
McIlroy looking for answers after squandered Masters lead

-
 McIlroy and Young share lead after Masters third round
McIlroy and Young share lead after Masters third round
-
Lavelle marks 100th cap with goal in US win over Japan

-
 Artemis crew urges unity on 'lifeboat' Earth
Artemis crew urges unity on 'lifeboat' Earth
-
US, Iran talks extend into second day as strait showdown deepens

-
 Former heavyweight king Fury outpoints Makhmudov, calls out Joshua
Former heavyweight king Fury outpoints Makhmudov, calls out Joshua
-
Former heavyweight king Fury outpoints Makhmudov on ring return

-
 Two-time champ Scheffler surges up Masters leaderboard
Two-time champ Scheffler surges up Masters leaderboard
-
McIlroy scrambles to hold off rivals and keep Masters lead

-
 Milan's Serie A title hopes in tatters after shock Udinese defeat, Juve fourth
Milan's Serie A title hopes in tatters after shock Udinese defeat, Juve fourth
-
Easter truce between Russia and Ukraine falters

-
 US warships transit Strait of Hormuz in mine clearance op
US warships transit Strait of Hormuz in mine clearance op
-
Playoff seedings on line as grueling NBA regular-season comes to close

-
 Ngumoha's 'special' impact no surprise to Slot
Ngumoha's 'special' impact no surprise to Slot
-
Arsenal suffer major title blow as Liverpool earn vital win

-
 US, Iran hold high-level peace talks in Pakistan
US, Iran hold high-level peace talks in Pakistan
-
Over 200 arrested at pro-Palestinian rally in London

-
 McIlroy tees off with six-stroke Masters lead
McIlroy tees off with six-stroke Masters lead
-
Record-breaking Bayern march closer to Bundesliga title

-
 World champions England make winning start to Women's Six Nations
World champions England make winning start to Women's Six Nations
-
Yamal shines as Barca thrash Espanyol to extend Liga lead

-
 Drean double sets Toulon up for Champions Cup semi against Leinster
Drean double sets Toulon up for Champions Cup semi against Leinster
-
Salah, Ngumoha ease Liverpool crisis with Fulham win


The New Age of Infiltration and the Collapse of Firewall-Based Security
NEW YORK, NY / ACCESS Newswire / November 21, 2025 / Around the world, nations are discovering that security now has two fronts. The physical front that protects borders, and the institutional front that protects trust. Governments poured resources into the first. The second has been left exposed. Institutions built on access and openness are now confronting threats that move quietly, slowly, and deliberately. They don't break rules. They use them. And that shift has created a global demand for a new kind of defense.
The exact type that SMX (NASDAQ:SMX) provides. Its technology closes the blind spots adversarial actors have exploited for years. The company has long warned that the next wave of security breaches would merge physical infiltration with digital manipulation, and today's patterns confirm that warning with precision.
Notably, these vulnerabilities aren't tied to any one country or ideology. They come from structural weaknesses in open systems built on participation and trust. That trust worked when threats were external, obvious, and easy to isolate. It doesn't hold when influence can hide inside the routines of institutional life. The infiltration of today is about access, not intrusion.
In other words, the compromise can be subtle. It doesn't trigger alarms or violate protocols. It enters through the everyday materials that move through supply chains, slipping in through components, parts, and products that appear routine. Once inside, it blends into operations until familiarity becomes its camouflage. That's the problem.
Most institutions lack the tools to verify where those materials truly originate, how they were handled, or whether they carry hidden vulnerabilities. SMX, now gaining deal traction across continents, is helping companies, institutions, and governments ensure those vulnerabilities never reach the point of catastrophe.
Where Physical Inputs and Digital Systems Converge
That protection starts with the obvious. Every modern threat begins with the physical. Bad actors understand that the easiest path into an institution is not through code or policy, but through the materials used. A single compromised component can enter a factory, a data center, a government lab, or a defense contractor long before cybersecurity systems ever activate. Once inside, that material becomes a trusted object, and trust becomes the attack surface.
From there, infiltration evolves. A corrupted chip can alter data. A counterfeit sensor can distort measurements. A compromised module can open digital pathways that no firewall was built to monitor. Physical infiltration becomes digital influence, and digital influence becomes institutional vulnerability. The chain starts with materials and ends with systems that no longer know what to trust.
This merger of physical access and digital impact is the defining threat of the modern era. It's not dramatic. It's procedural. It uses supply-chain familiarity to validate inputs, and those inputs to manipulate downstream information and operations. To truly be secured, that chain must be fortified at every link. SMX provides the technology to do that.
The SMX System is Built for Both Dimensions of Modern Security
SMX secures the physical world by giving materials, documents, and products a molecular identity. It embeds memory and provenance into the item itself. It can be gold, rubber, liquids, or textiles. Virtually any material can benefit. Once embedded, tampering becomes impossible to hide. Counterfeits become easy to expose. Origins remain inseparable from the objects they belong to.
This has always been SMX's foundation, and as new threats emerge, its technology is showing it can be an essential part of global stability protocols. No, SMX cannot control what people think. But it can eliminate the deception that enables influence. It verifies the provenance of the materials, credentials, and hardware entering a system, making manipulation transparent and infiltration visible. That is how it defends. And by securing every link in the chain, that capability becomes the impenetrable piece of the arsenal that protects both critical assets and the people who depend on them.
About SMX
As global businesses face new and complex challenges related to carbon neutrality and meeting governmental and regional regulations and standards, SMX can offer players along the value chain access to its marking, tracking, measurement, and digital platform technology to transition more successfully to a low-carbon economy.
Forward-Looking Statements
This editorial contains forward-looking statements that involve significant risks and uncertainties. These statements reflect current views regarding the potential use of SMX technology to enhance institutional integrity, strengthen verification systems, and reduce the risk of infiltration by bad actors or nefarious networks. Forward-looking statements include, but are not limited to, statements regarding anticipated improvements in institutional security, the possible adoption of molecular-level verification, the ability of SMX systems to protect credentials, documents, or access pathways, and the broader market or regulatory conditions that may influence demand for such solutions. These statements are based on assumptions that may prove inaccurate and are subject to factors that are difficult to predict. Actual results may differ materially from those expressed or implied due to a range of uncertainties, including changes in government policy, evolving threat landscapes, institutional readiness, regulatory considerations, funding cycles, technological constraints, and other risks detailed in SMX's filings with the Securities and Exchange Commission.
Forward-looking statements speak only as of the date of this editorial. Readers should not place undue reliance on them. SMX undertakes no obligation to update or revise any forward-looking statements to reflect new information, future events, or changes in circumstances except as required by law. The purpose of this content is to explore potential applications of verification technologies within institutional environments. Nothing in this editorial should be interpreted as a guarantee of future performance or a prediction of specific security outcomes.
EMAIL: [email protected]
SOURCE: SMX (Security Matters) Public Limited
View the original press release on ACCESS Newswire
H.Gonzales--AT

